Linux Commands – 21 Common Linux Tips and Tricks
As we learn and more about Linux we tend to gain more expertise working on Linux command line. I’ve been working on Linux command line for last 7 years from now and learned many cool tricks that can save your time and make your life a lot easier. This article will cover 21 Common Linux Tips and Tricks which will hopefully benefit you.
NOTE – All the examples in this article are tested on bash shell powered by Rackhansa’s Virtual Private Server.
1. How switch between directories more efficiently
When we’re working in Linux shell environment, we’ve to switch between directories very often. Let’s suppose if you’re in directory /var/log/httpd/ and then you move to directory /home/alice/. Now you’d want to switch back to directory /var/log/httpd/. To switch back to /var/log/httpd/ by typing its complete path can be bothersome. For this we will use command “cd -” short cut.
The correct method to use this short cut is first go to your directory (a) for instance /var/log/httpd/ and now type command “pwd” and then go to directory (b) for instance /home/ and now type “cd -” and it should bring you back to /var/log/httpd/.
Let’s experiment this on Linux command line by following the below example:
$ pwd /var/log/httpd
$ cd /home/
$ cd - /var/log/httpd
Looks nifty enough, eh ? but the fact is that “cd -” will only benefit us partially as it can switch between two directories only. And if ou want to switch between multiple directories then we’d use more commands to achieve this task, such as combination of command “pushd” and “popd”. These Linux command will work as follow:
Suppose if you’re at directory (a) and then you switch to directory (b) then (c) then (d) and then (e) and now you want to go back to directory (a), then these commands will help you with this hurdle.
Below is given live example of these Linux commands:
$ cd /var/log/ $ pwd /var/log $ pushd /var/www/ /var/www /var/www $ cd /home/ $ cd /etc/ $ cd /proc/ $ popd /var/www $ pwd /var/log
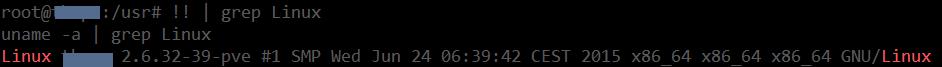
2. How to use !! and ! to make the history command work more efficiently ?
Double exclamation mark “!!” will run the last command typed on shell and it will also display it’s result again :
$ echo "hi this is the command i typed last" hi this is the command i typed last $ !! echo "hi this is the command i typed last" hi this is the command i typed last
Here’s how we can use this command more efficiently :
$ uname -a Linux testdomain 2.6.32-39-pve #1 SMP Wed Jun 24 06:39:42 CEST 2015 x86_64 x86_64 x86_64 GNU/Linux
$ !! | grep Linux Linux testdomain 2.6.32-39-pve #1 SMP Wed Jun 24 06:39:42 CEST 2015 x86_64 x86_64 x86_64 GNU/Linux
Now we’ll discuss what the single exclamation mark “!” does. “!!” will only run previously run command but single exclamation “!” has various functions of recalling the previously entered commands such as it will access any command entered by reading the “history” command database. For instance, if you run the “history” command, it will display list of commands ran on the system with serial number prefixed to each command. So, the single “!” exclamation command will be used as a prefix to the serial number corresponding to that command line. See the example given below:
$ history ... ... ... 2039 uname -a | grep Linux 2040 dmesg 2041 clear 2042 cd bin 2043 clear 2044 pwd 2045 touch new_binary 2046 sudo touch new_binary 2047 ls new_binary 2048 history
$ !2039 uname -a | grep Linux Linux himanshu-Inspiron-1525 3.2.0-36-generic-pae #57-Ubuntu SMP Tue Jan 8 22:01:06 UTC 2013 i686 i686 i386 GNU/Linux
As we can see it ran the command with serial number 2039. And now in another example we will use “!” command to recall last command typed in combination to current command:
$ echo 127.0.0.1 $ ping !$ ping 127.0.0.1 PING 127.0.0.1 (127.0.0.1) 56(84) bytes of data. 64 bytes from 127.0.0.1: icmp_seq=1 ttl=64 time=0.030 ms 64 bytes from 127.0.0.1: icmp_seq=2 ttl=64 time=0.017 ms 64 bytes from 127.0.0.1: icmp_seq=3 ttl=64 time=0.017 ms
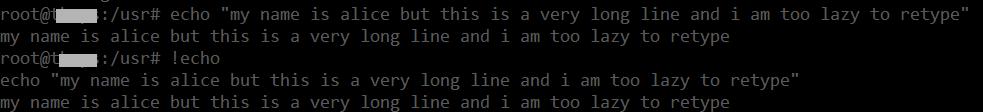
And we can also use “!” command in combination with ‘keyword’ of last command typed (in case if last typed command was too long) :
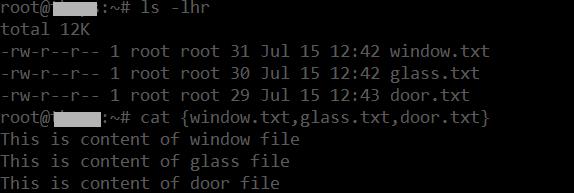
3. How to Use comma “,” operator to makes life easier
There are few functions of “,” comma operator we can utilize to make our life easier.
Convert to lower case
Comma operator can be used to either convert the whole string or only the first letter to lower case.
$ phrase="My Country is GERMANY"
$ echo ${phrase,}
my Country is GERMANY $ echo ${phrase,,}
my country is germany Using comma operator with file names
Comma operator can be used to input more than single file names
4. How to delete files with spaces in them or at the end of file name
Deleting files with spaces in the middle of them or at the end can be tricky for newbies and it may give following error :
$ rm map of russia.jpg rm: cannot remove 'map': No such file or directory rm: cannot remove 'of': No such file or directory rm: cannot remove 'russia.jpg': No such file or directory
To tackle this issue we have two options. (a) use double quotes :
$ rm "map of russia.jpg"
(b) we can use back slash “” along with space :
$ rm map of russia.jpg
5. How to delete files with names starting with dash or hyphen (-)
Deleting files with hyphen as prefix can be tricky and it won’t work with the trick described previously
$ rm -2filenamewith.hyphen rm: invalid option -- '2' Try `rm ./-2filenamewith.hyphen' to remove the file `-2filenamewith.hyphen'. Try `rm --help' for more information.
It won’t work even with double quotes :
rm "-2filenamewith.hyphen" rm: invalid option -- '2' Try `rm ./-2filenamewith.hyphen' to remove the file `-2filenamewith.hyphen'. Try `rm --help' for more information.
6. How to delete all of the files in a directory except for some selected files
Here is a directory containing lot of files : In this tip we will learn how to delete all of the files in a directory except for some selected files (specially if they have different file extensions) :
$ ls put.out Cppfile.c filetype.c macrom.c myprintf.c orignal_file.orig mashup.c blowfish.c cmdline.c firstPYtProgram.py main.c newprintf.c orignal_file.rej test_stracefile.c blewfish.c envo.c helloworldprog.c myfopen.c newwork.txt progy.c virtual_function.c
Now if you want to delete every file except for .c and .py files,
This is what you’d do :
$ rm !(*.c|*.py) $ ls Cppfile.c filetype.c macrom.c myprintf.c mashup.c blowfish.c cmdline.c firstPYtProgram.py main.c newprintf.c test_stracefile.c blewfish.c envo.c helloworldprog.c myfopen.c progy.c virtual_function.c
As you can see that files with other extensions have been deleted with the following command combination.
7. How to use tail command efficiently
As we know we can use the tail command instead of cat command to view only the last part of the file. But we can also use tail command to see the last result of a command that results in numerous lines. For instance your iptables list could be a large one :
$ iptables -nL Chain INPUT (policy ACCEPT) target prot opt source destination DROP all -- 58.30.0.0/16 0.0.0.0/0 DROP all -- 187.33.0.0/19 0.0.0.0/0 DROP all -- 113.196.0.0/16 0.0.0.0/0 DROP all -- 190.167.0.0/16 0.0.0.0/0 DROP all -- 202.46.0.0/16 0.0.0.0/0 DROP all -- 202.104.0.0/16 0.0.0.0/0 DROP all -- 66.135.34.113 0.0.0.0/0 DROP all -- 80.0.0.0/4 0.0.0.0/0 /* RIPEurope */ DROP all -- 178.0.0.0/8 0.0.0.0/0 /* RIPEurope */ DROP all -- 91.0.0.0/8 0.0.0.0/0 /* RIPEurope */ DROP all -- 77.0.0.0/8 0.0.0.0/0 /* RIPEurope */ DROP all -- 46.0.0.0/8 0.0.0.0/0 /* RIPEurope */ DROP all -- 188.0.0.0/8 0.0.0.0/0 /* RIPEurope */ DROP all -- 37.0.0.0/8 0.0.0.0/0 /* RIPEurope */ DROP all -- 193.0.0.0/8 0.0.0.0/0 /* RIPEurope */ DROP all -- 2.0.0.0/8 0.0.0.0/0 /* RIPEurope */ DROP all -- 5.0.0.0/8 0.0.0.0/0 /* RIPEurope */ DROP all -- 31.0.0.0/8 0.0.0.0/0 /* RIPEurope */ DROP all -- 62.0.0.0/8 0.0.0.0/0 /* RIPEurope */ DROP all -- 93.0.0.0/8 0.0.0.0/0 /* RIPEurope */ DROP all -- 95.0.0.0/8 0.0.0.0/0 /* RIPEurope */ DROP all -- 109.0.0.0/8 0.0.0.0/0 /* RIPEurope */ DROP all -- 176.0.0.0/8 0.0.0.0/0 /* RIPEurope */ DROP all -- 217.0.0.0/8 0.0.0.0/0 /* RIPEurope */ DROP all -- 92.0.0.0/8 0.0.0.0/0 /* RIPEurope */ DROP all -- 78.0.0.0/7 0.0.0.0/0 /* RIPEurope */ DROP all -- 213.0.0.0/8 0.0.0.0/0 /* RIPREurope */ DROP all -- 130.185.0.0/16 0.0.0.0/0 /* RIPREurope */ DROP tcp -- 0.0.0.0/0 0.0.0.0/0 source IP range 22 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 220.191.0.1-220.191.127.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 220.192.0.1-220.207.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 220.242.0.1-220.242.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 220.248.0.1-220.248.127.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 220.250.0.1-220.250.0.7 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 220.252.0.1-220.252.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 221.0.0.1-221.3.127.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 221.122.0.1-221.122.3.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 221.176.0.1-221.183.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 221.192.0.1-221.195.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 221.200.0.1-221.203.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 221.204.0.1-221.205.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 221.206.0.1-221.206.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 221.207.0.1-221.207.63.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 221.208.0.1-221.212.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 221.208.0.1-221.212.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 221.214.0.1-221.214.0.127 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 221.216.0.1-221.223.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 221.0.0.1-221.255.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 221.224.0.1-221.231.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 221.224.0.1-221.231.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 221.232.0.1-221.235.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 222.32.0.1-222.63.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 222.64.0.1-222.64.3.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 222.80.0.1-222.83.127.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 222.132.0.1-222.135.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 222.136.0.1-222.143.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 222.168.0.1-222.169.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 222.172.222.1-222.172.222.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 222.176.0.1-222.183.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 222.184.0.1-222.191.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 222.200.0.1-222.200.31.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 222.208.0.1-222.215.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 222.219.0.1-222.221.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 222.240.0.1-222.240.63.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 223.4.0.1-223.7.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 223.64.0.1-223.117.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 223.144.0.1-223.159.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 223.240.0.1-223.247.255.254 Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination
Now if we want to see only last few list of the iptables filter then we’d use following command :
$ iptables -nL | tail DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 223.4.0.1-223.7.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 223.64.0.1-223.117.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 223.144.0.1-223.159.255.254 DROP all -- 0.0.0.0/0 0.0.0.0/0 source IP range 223.240.0.1-223.247.255.254 Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination
So using the command tail at the end of iptables -nL will only display last few lines of the result from this command.
8. Why rm command sometimes fails with error “Argument list too long”
This usually happens when you have a directory containing huge number of files. When you do a rm -rf over it, you get something like : “Argument list too long”.
-bash: /bin/rm: Argument list too long
This error can be rectified using the following command (before trying this command make sure to enter the directory which has huge amount of files stored in it) :
find * -xdev -exec rm -f '{}' ';' This is the fastest method to delete large amount of files as it supplies input to rm command in batches to process.
9. How to check which Linux distribution you are using
Sometimes when you’re on a VPS server and you want to double check that you’re using the right distribution as promised (or in any other case you’d want to know that which distro are you using) you can use the following command :
$ cat /etc/*-release DISTRIB_ID=Ubuntu DISTRIB_RELEASE=14.04 DISTRIB_CODENAME=trusty DISTRIB_DESCRIPTION="Ubuntu 14.04.2 LTS" NAME="Ubuntu" VERSION="14.04.2 LTS, Trusty Tahr" ID=ubuntu ID_LIKE=debian PRETTY_NAME="Ubuntu 14.04.2 LTS" VERSION_ID="14.04" HOME_URL="http://www.ubuntu.com/" SUPPORT_URL="http://help.ubuntu.com/" BUG_REPORT_URL="http://bugs.launchpad.net/ubuntu/"
As you can see that there’s a file in /etc/ directory that contains version and distribution details. However as you can see in the result that the above command did not only revealed the distro name and version it also provided additional information as well, but in case if you want to know the distro and version only then for some distro (specially Ubuntu and Debian) we can use the following command :
$ cat /etc/*-release | grep VERSION VERSION="14.04.2 LTS, Trusty Tahr" VERSION_ID="14.04"
Using grep VERSION (case sensitive) will only extract version line from that file and it will contain complete version+distro name
There maybe some files which you wouldn’t want to delete but only flush its’ content, log files can be a great example of such file. So below command will erase only the content of the file while keeping the file it self intact :
$ > (complete path of file)
For e.g.
$ > /var/log/apache2/access.log
This command will only flush the content of the file “access.log” without deleting the file itself
11. How we can search man pages for a particular string?
*nix man pages are manual pages for *nix commands as they provide detailed and thorough instructions and information about the command whose man-page you are looking it. But, let’s suppose if you want to know which man page has the content about a particular topic. Such as, if you want to know which man pages discuss about string “windows” ?
Hmmm, in this case we can use option -k with man command which can let you do this :
$ man -k windows fixwfwps (1) - filter to fix Word for Windows documents so PSUtils work fixwwps (1) - filter to fix Windows Write documents so PSUtils work samba (7) - A Windows AD and SMB/CIFS fileserver for UNIX windmc (1) - generates Windows message resources.
As we can see that any man page containing string “windows” were displayed in the result.
Suppose if you want to create a new file with minimal content and you don’t want to open a text/file editor. Here’s what you will do to achieve this task :
$ echo a dummy file with so little content > small.file
Now let’s test it
$ cat small.file a dummy file with so little content
Another function of this operator can be, using it to save the output/result of a particular command. For instance :
$ ping google.com -c 4 > google_ping.out
Let’s test this one as well :
$ cat google_ping.out PING google.com (173.194.113.46) 56(84) bytes of data. 64 bytes from fra02s20-in-f14.1e100.net (173.194.113.46): icmp_seq=1 ttl=53 time=12.3 ms 64 bytes from fra02s20-in-f14.1e100.net (173.194.113.46): icmp_seq=2 ttl=53 time=12.4 ms 64 bytes from fra02s20-in-f14.1e100.net (173.194.113.46): icmp_seq=3 ttl=53 time=12.5 ms 64 bytes from fra02s20-in-f14.1e100.net (173.194.113.46): icmp_seq=4 ttl=53 time=12.3 ms --- google.com ping statistics --- 4 packets transmitted, 4 received, 0% packet loss, time 3003ms rtt min/avg/max/mdev = 12.309/12.387/12.506/0.134 ms
13. How to use tail command to view multiple files on the go
There are certain files we’d like to view one by one but with one go. Specially if their last few lines are import, so for such task we will use the following command :
$ tail -f google_ping.out yahoo_ping.out bing_ping.out ==> google_ping.out <== PING google.com (173.194.113.32) 56(84) bytes of data. 64 bytes from fra02s20-in-f0.1e100.net (173.194.113.32): icmp_seq=1 ttl=53 time=12.4 ms 64 bytes from fra02s20-in-f0.1e100.net (173.194.113.32): icmp_seq=2 ttl=53 time=12.2 ms --- google.com ping statistics --- 2 packets transmitted, 2 received, 0% packet loss, time 1000ms rtt min/avg/max/mdev = 12.287/12.389/12.491/0.102 ms ==> yahoo_ping.out <== PING yahoo.com (206.190.36.45) 56(84) bytes of data. 64 bytes from ir1.fp.vip.gq1.yahoo.com (206.190.36.45): icmp_seq=1 ttl=49 time=153 ms 64 bytes from ir1.fp.vip.gq1.yahoo.com (206.190.36.45): icmp_seq=2 ttl=49 time=153 ms --- yahoo.com ping statistics --- 2 packets transmitted, 2 received, 0% packet loss, time 1188ms rtt min/avg/max/mdev = 153.010/153.116/153.222/0.106 ms ==> bing_ping.out <== PING bing.com (204.79.197.200) 56(84) bytes of data. 64 bytes from a-0001.a-msedge.net (204.79.197.200): icmp_seq=1 ttl=117 time=5.00 ms 64 bytes from a-0001.a-msedge.net (204.79.197.200): icmp_seq=2 ttl=117 time=4.65 ms --- bing.com ping statistics --- 2 packets transmitted, 2 received, 0% packet loss, time 999ms rtt min/avg/max/mdev = 4.657/4.831/5.006/0.187 ms
As we can see that each file has it’s caption/heading before its’ output
14. How to type a command and hide it to show up in the output of “history” command?
Sometimes you’ve to use a loop of commands and you don’t want to flood your linux “history” with these command as it will flush all oldest records. To achieve this task we’ll follow below procedure :
$ df -h $ du -h $ ping google.com -c 4
Please note that there’s an extra space between “$” and “ping” but there isn’t any extra space between df and du commands, hence putting extra space before the actual command will make it hide from showing up in the history command.
Let’s test it :
$ history | tail 242 df -h 243 du -h 244 history | tail
As it can be seen that not only “ping” command is hidden from history but also the serial number in history commands doesnt change, making that command completely stealth.
15. How to make the output of a command to display in slow motion
Sometimes when we’re typing specific commands, the output of that command can come and go so quickly that you may not be able to see what actually was displayed. To tackle this issue we can use the following command which will slow down the output speed :
$ last | pv -qL 25
Try this command at your end for more realistic results
16. How to block a string from IPTables
Sometimes blocking a specific string can be a lot of time saving than blocking plenty of ip addresses trying to attack your server with same string. For example “wp-login.php”. There maybe hundred of IP addresses who tried this string on your web server but blocking all of the IP addresses who tried this string can be stupid sometimes. Instead we can simply block that string instead which is used by most of the attackers (or script kiddies). To achieve this task we’ll use the following switches and options of iptables command :
$ iptables -A INPUT -p tcp --dport 80 -m string --algo bm --string 'c' -j DROP
This command will block any string containing “/wp-login.php” in it over port 80 (which is a common port of Linux web server such as Apache2)
17. How to delete a file if it’s being used by the system
Sometimes when we have to delete a file, but it doesn’t get deleted because it’s usually being used by another program. In order to delete such files forcefully we will stop that file using the fuser command :
$ fuser -k <filename>
And once the file is stopped (no longer in use by the system) we can then easily delete that file without any error messages.
18. How to save result of a command while monitoring its output at the same time
As we know that “>” operator can be used to record/save the output of a command. But we can also save the output of a command while monitoring its output in real-time as well.
Here’s what we’ll have to type :
$ ping google.com -c 3 | tee google_ping.out PING google.com (173.194.113.39) 56(84) bytes of data. 64 bytes from fra02s20-in-f7.1e100.net (173.194.113.39): icmp_seq=1 ttl=56 time=12.2 ms 64 bytes from fra02s20-in-f7.1e100.net (173.194.113.39): icmp_seq=2 ttl=56 time=12.4 ms 64 bytes from fra02s20-in-f7.1e100.net (173.194.113.39): icmp_seq=3 ttl=56 time=12.3 ms --- google.com ping statistics --- 3 packets transmitted, 3 received, 0% packet loss, time 2002ms rtt min/avg/max/mdev = 12.219/12.338/12.456/0.160 ms
19. How to check if the command last typed was succeeded or failed?
Here is an example :We can achieve this task by typing “$?” exactly right after typing the command. If the command was successful it would return “0” value. But if it failed then it will return any value other than “0” i.e. higher than “0”.
$ touch xyz touch: cannot touch `xyz': Permission denied
$ echo $? 1
As the value is greater than 0, it means it wasn”t successful. Furthermore we can also see “permission denied” error
20. How to copy paste in a shell environment through keyboard?
First you’d select the text to copy and then press Ctrl + SHIFT + C keys, this will copy the text. And when you’d desire to paste the copied text you’ll simply type Ctrl + SHIFT + V keys, and this will paste it.
Please note that this may not work with putty.exe program
21. How to search for all the files in the current directory containing a specific string?
This task can be easily achieved using -l switch with grep command :
$ grep -l "printf" *.c blowfish.c helloworld.c mangler.c pingfast.c
Feel free to contact us if you believe you’re still facing issues following these steps. Rackhansa Professionals are always ready to help their customers in making their online presence smooth and uninterrupted. Our free webhosting services have also been devised mainly for those entrepreneurs who have just jumped into online business. To know more about our services, please visit our products page to enjoy the cheap hosting plans.